SquidGrow
Smart Contract Audit Report
Audit Summary
 SquidGrow is a new BEP-20 token on the Binance Smart Chain that is an automatic liquidity providing protocol.
SquidGrow is a new BEP-20 token on the Binance Smart Chain that is an automatic liquidity providing protocol.
For this audit, we reviewed the project team's SquidGrow contract at 0x88479186BAC914E4313389a64881F5ed0153C765 on the Binance Smart Chain Mainnet.
Audit Findings
Low findings were identified and the team should consider resolving these issues. In addition, centralized aspects are present.
Date: June 27th, 2022.Finding #1 - SquidGrow - Low
Description: The swapAndLiquify() function transfers BNB from the contract to the team's fee wallets using thetransfer()function instead of thecall()function.
Risk/Impact: Thetransfer()function uses a hardcoded gas amount of 2300, meaning transactions could run out of gas as the team receives BNB if the receiver is a contract.
Recommendation: The team should ensure that the receiver addresses are not smart contracts, or use.call.value{...}("")instead as it does not have a gas limitation.
Resolution: The team has not yet addressed this issue.
Finding #2 - SquidGrow - Informational
Description: The checkBot() function contains the following issues:
- This isCont() check can be bypassed through a contract's constructor as a contract's Assembly extcodesize size is equal to 0 when deploying.
- The Pair address will be added to the Anti-bot list when a user is attempting to buy tokens before the contract start time.
- The following check is redundant as the Pair address should always be set to true in the
isInternalmapping:sender == pair && botOn && !isInternal[sender] && msg.sender != tx.origin.
Risk/Impact: The isCont() function can be bypassed making it possible for contract addresses to transfer tokens. The Pair address will be added to the Anti-bot list when a user is attempting to buy tokens before the contract start time, which will increase fees to 99% on all buy and sell transactions.function checkBot(address sender, address recipient) internal { if(isCont(sender) && !isInternal[sender] && botOn || sender == pair && botOn && !isInternal[sender] && msg.sender != tx.origin || startedTime > block.timestamp){isBot[sender] = true;} if(isCont(recipient) && !isInternal[recipient] && !isFeeExempt[recipient] && botOn || sender == pair && !isInternal[sender] && msg.sender != tx.origin && botOn){isBot[recipient] = true;} }
Recommendation: As the contract is already deployed, we recommend that the team never reset the contract start time and never enables the Anti-bot functionality. The checkBot() function should be modified to checkmsg.sender != tx.originto verify that the address participating in a transfer is not a contract, remove the redundant check above, and ensure that the Pair address will never be added to the Anti-bot list. The checkbot() function could be modified as follows:
function checkBot(address sender, address recipient) internal { if(botOn && msg.sender != tx.origin && (!isInternal[sender] || !isInternal[recipient]) && !isFeeExempt[recipient] || startedTime > block.timestamp) { isBot[tx.origin] = true; if (!isInternal[msg.sender]) { isBot[msg.sender] = true; } } }
Finding #3 - SquidGrow - Informational
Description: Although the SafeMath library is utilized, the contract is deployed with Solidity v0.8.14 which has built-in overflow checks.
Recommendation: SafeMath could safely be removed to reduce contract size, deployment costs, and gas costs on all transactions that utilize it.
Finding #4 - SquidGrow - Informational
Description: Several state variables cannot be modified, but are not declared constant.
Recommendation: These state variables should be declared constant for additional gas savings on each reference.DEAD, _totalSupply, feeDenominator, minSells, swapTimer
Contract Overview
Ownership Controls:
- The total supply of the token is set to 1 quadrillion $SquidGrow [1,000,000,000,000,000].
- No mint or burn functions are present, though the circulating supply can be decreased by sending tokens to the 0x..dead address.
- At the time of writing this report, there are 3,808 total token holders. The token allocation is as follows:
- 26.26% of the total supply belongs to the team's Farm contract. This contract was not in scope for this audit.
- 13.59% of the total supply belongs to a wallet controlled by the team.
- The next five EOAs own a cumulative 16.04% of the total supply.
- 11.2% of the total supply is in Pancakeswap liquidity.
- Of that liquidity, 71.4% of the LP tokens are stored in an unverified contract.
- 27.39% of the LP tokens belong to the team's Farm contract.
- The team must manually enable trading before all token transfers can take place on the platform. Only users that have been exempt from fees can participate in transfers when trading is disabled. Once trading is enabled, it can never be disabled.
- The contract enforces a maximum wallet amount that prevents a transfer from occurring if the recipient's token balance will exceed the limit number of tokens (set by the team) after the transfer occurs.
- The contract enforces a maximum transaction amount (set by the team) which imposes a limit to the number of tokens that can be transferred during any given transaction.
- The contract features an Anti-Bot mechanism that is triggered when any contract that has not been excluded by the team is either the sender or the recipient of a transfer or when a user attempts to transfer tokens before the start time of the contract has been reached. The Anti-bot functionality contains logical issues as identified in Finding #2.
- Accounts that have been added to the Anti-bot list will be taxed at a 99% rate.
- There is a Liquidity fee, Marketing fee, Staking fee, and Burn fee on all transfers where neither the sender nor the recipient is excluded from fees.
- Fees are increased on all non-buy transactions by the transfer percentage set by the team.
- The tokens collected through fees are stored in the contract address. The tokens are swapped for BNB for the purpose of funding Pancakeswap liquidity when the following conditions are met:
- More than 150 billion tokens are being transferred.
- The threshold number of tokens (set by the team) in the contract address has been reached.
- The automatic liquidity add functionality is currently enabled.
- The contract is not currently performing an automatic liquidity add.
- The caller is not initiating a buy transaction.
- At least 7 sell transactions and peer-to-peer transfers have occurred since this functionality has previously occurred.
- Liquidity-adds are automatically performed by selling the tokens collected as fees, pairing the received BNB with the token, and adding it as liquidity to the BNB pair.
- The LP tokens received through this process are sent to the Liquidity address set by the team. We recommend that the team lock these newly acquired LP tokens.
- The tokens collected through the Marketing fee and Staking fee are swapped for BNB and sent to the team's Marketing address and Staking address respectively.
- The tokens collected through the Burn fee are sent to the 0x..dead address.
- The contract's full BNB balance will be split amongst 4 wallets controlled by the team when less than 2 tokens are transferred to a Distributor address set by the team.
- The contract's full LP token balance will be sent to a wallet controlled by the team when between 2 and 3 tokens are transferred to a Distributor address set by the team.
- As the contract is deployed with Solidity v0.8.14, it is protected from overflows/underflows.
- The contract complies with the BEP-20 token standard.
- The team can assign addresses to an Authorized role that is used to maintain control of various role-restricted functions within the contract.
- Authorized addresses can set total fees up to 10% at any time.
- Authorized addresses can set the additional fee on all non-buy transactions to any percentage at any time.
- Authorized addresses can include and exclude accounts from transfer fees and the maximum transaction limit.
- Authorized addresses can enable/disable the Anti-bot mechanism at any time.
- Authorized addresses can add/remove accounts from the Anti-bot list at any time.
- Authorized addresses can set the maximum wallet amount and maximum transaction amount to any values greater than 5 trillion tokens.
- Authorized addresses can update the amount of BNB that gets allocated to the Marketing fund, Staking fund, and Liquidity fund to any values at any time.
- Authorized addresses can update the start time of the contract at any time.
- Authorized addresses can withdraw any tokens from the contract at any time.
- Authorized addresses can split all of the BNB in the contract amongst 4 wallets controlled by the team at any time.
- Authorized addresses can send any amount of BNB from the contract to the team's Default address.
- Authorized addresses can withdraw any of the LP tokens in the contract at any time.
- Authorized addresses can enable/disable automatic liquidity adds at any time.
- Authorized addresses can set the threshold number of tokens that triggers an automatic liquidity add to any value at any time.
- Authorized addresses can add accounts as an internal address which excludes the address from the Anti-bot mechanism, Maximum wallet limit, transfer counter logic, and swapback logic at any time.
- Authorized addresses can update the team's Liquidity address, Marketing address, Staking address, Default address, and 4 team wallets to any addresses at any time.
Audit Results
| Vulnerability Category | Notes | Result |
|---|---|---|
| Arbitrary Jump/Storage Write | N/A | PASS |
| Centralization of Control |
|
WARNING |
| Compiler Issues | N/A | PASS |
| Delegate Call to Untrusted Contract | N/A | PASS |
| Dependence on Predictable Variables | N/A | PASS |
| Ether/Token Theft | N/A | PASS |
| Flash Loans | N/A | PASS |
| Front Running | The automatic token swapping functionality may be susceptible to front-running; The team must monitor and if suspicious activity is detected, the team should lower the swapThreshold value or disable this system altogether. |
PASS |
| Improper Events | N/A | PASS |
| Improper Authorization Scheme | N/A | PASS |
| Integer Over/Underflow | N/A | PASS |
| Logical Issues | The checkBot() function contains multiple issues as identified in Finding #2. | WARNING |
| Oracle Issues | N/A | PASS |
| Outdated Compiler Version | N/A | PASS |
| Race Conditions | N/A | PASS |
| Reentrancy | N/A | PASS |
| Signature Issues | N/A | PASS |
| Unbounded Loops | N/A | PASS |
| Unused Code | N/A | PASS |
| Overall Contract Safety | PASS |
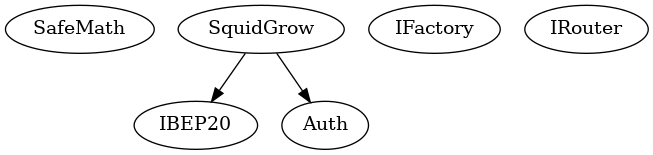
Inheritance Chart
Function Graph
Functions Overview
($) = payable function
# = non-constant function
Int = Internal
Ext = External
Pub = Public
+ [Lib] SafeMath
- [Int] add
- [Int] sub
- [Int] mul
- [Int] div
- [Int] mod
- [Int] tryAdd
- [Int] trySub
- [Int] tryMul
- [Int] tryDiv
- [Int] tryMod
- [Int] sub
- [Int] div
- [Int] mod
+ [Int] IBEP20
- [Ext] totalSupply
- [Ext] decimals
- [Ext] symbol
- [Ext] name
- [Ext] balanceOf
- [Ext] transfer #
- [Ext] allowance
- [Ext] approve #
- [Ext] transferFrom #
+ Auth
- [Pub] #
- [Pub] authorize #
- modifiers: authorized
- [Pub] unauthorize #
- modifiers: authorized
- [Pub] isOwner
- [Pub] isAuthorized
- [Pub] transferOwnership #
- modifiers: authorized
- [Ext] renounceOwnership #
- modifiers: authorized
+ [Int] IFactory
- [Ext] createPair #
- [Ext] getPair
+ [Int] IRouter
- [Ext] factory
- [Ext] WETH
- [Ext] addLiquidityETH ($)
- [Ext] swapExactETHForTokensSupportingFeeOnTransferTokens ($)
- [Ext] swapExactTokensForETHSupportingFeeOnTransferTokens #
+ SquidGrow (IBEP20, Auth)
- [Pub] #
- modifiers: Auth
- [Ext] ($)
- [Pub] name
- [Pub] symbol
- [Pub] decimals
- [Pub] totalSupply
- [Pub] balanceOf
- [Pub] transfer #
- [Pub] allowance
- [Pub] viewisBot
- [Int] isCont
- [Pub] approve #
- [Pub] getCirculatingSupply
- [Ext] setFeeExempt #
- modifiers: authorized
- [Ext] setisBot #
- modifiers: authorized
- [Ext] setisInternal #
- modifiers: authorized
- [Ext] setbotOn #
- modifiers: authorized
- [Ext] syncContractPair #
- modifiers: authorized
- [Ext] approvals #
- modifiers: authorized
- [Ext] setPairReceiver #
- modifiers: authorized
- [Ext] setstartSwap #
- modifiers: authorized
- [Ext] setSwapBackSettings #
- modifiers: authorized
- [Pub] transferFrom #
- [Prv] _approve #
- [Prv] _transfer #
- [Int] preTxCheck
- [Int] checkStartSwap
- [Int] checkMaxWallet
- [Int] transferCounters #
- [Int] shouldTakeFee
- [Int] taxableEvent
- [Int] taketotalFee #
- [Pub] getTotalFee
- [Int] checkTxLimit
- [Int] checkBot #
- [Ext] approval #
- modifiers: authorized
- [Int] checkapprovals #
- [Ext] setMaxes #
- modifiers: authorized
- [Int] syncPair #
- [Ext] rescueBEP20 #
- modifiers: authorized
- [Ext] setExemptAddress #
- modifiers: authorized
- [Ext] setDivisors #
- modifiers: authorized
- [Int] performapprovals #
- [Ext] setStructure #
- modifiers: authorized
- [Ext] setInternalAddresses #
- modifiers: authorized
- [Int] shouldSwapBack
- [Int] swapBack #
- [Prv] swapAndLiquify #
- modifiers: lockTheSwap
- [Prv] addLiquidity #
- [Prv] swapTokensForBNB #
About SourceHat
SourceHat has quickly grown to have one of the most experienced and well-equipped smart contract auditing teams in the industry. Our team has conducted 1800+ solidity smart contract audits covering all major project types and protocols, securing a total of over $50 billion U.S. dollars in on-chain value!
Our firm is well-reputed in the community and is trusted as a top smart contract auditing company for the review of solidity code, no matter how complex. Our team of experienced solidity smart contract auditors performs audits for tokens, NFTs, crowdsales, marketplaces, gambling games, financial protocols, and more!
Contact us today to get a free quote for a smart contract audit of your project!
What is a SourceHat Audit?
Typically, a smart contract audit is a comprehensive review process designed to discover logical errors, security vulnerabilities, and optimization opportunities within code. A SourceHat Audit takes this a step further by verifying economic logic to ensure the stability of smart contracts and highlighting privileged functionality to create a report that is easy to understand for developers and community members alike.
How Do I Interpret the Findings?
Each of our Findings will be labeled with a Severity level. We always recommend the team resolve High, Medium, and Low severity findings prior to deploying the code to the mainnet. Here is a breakdown on what each Severity level means for the project:
- High severity indicates that the issue puts a large number of users' funds at risk and has a high probability of exploitation, or the smart contract contains serious logical issues which can prevent the code from operating as intended.
- Medium severity issues are those which place at least some users' funds at risk and has a medium to high probability of exploitation.
- Low severity issues have a relatively minor risk association; these issues have a low probability of occurring or may have a minimal impact.
- Informational issues pose no immediate risk, but inform the project team of opportunities for gas optimizations and following smart contract security best practices.
