Vault Genesis
Smart Contract Audit Report
Audit Summary
 Factor DAO is creating a new Vault which swaps deposited funds for various underlying assets.
Factor DAO is creating a new Vault which swaps deposited funds for various underlying assets.
For this audit, we reviewed Factor DAO's VaultGenesis contract at commit 3cf300777bd4f8bed0080ee830c9b0312daf30e2 on the team's private GitHub repository.
We previously reviewed the project team's platform here.
Audit Findings
No findings were identified, though some centralized aspects are present.
Date: March 28th, 2023.
Contract Overview
- As the contracts are implemented with Solidity v0.8.0, they are safe from any possible overflows/underflows.
- The team must exercise caution when assigning the staking token to avoid using fee-on-transfer tokens unless the proper exemptions are made.
- This contract allows users to deposit a specified staking token which is then swapped for various tokens and stored within the contract.
- Deposits cannot be made until the Vault Manager or Governor "starts" the Vault.
- When a deposit is made, the user's tokens are transferred into this contract where they are split into portions and swapped for various underlying assets.
- The user specifies a minimum share amount to receive, as well as data to be used for the swap.
- Swaps are made using an associated OpenOceanExchange contract, which was not included in the scope of this audit.
- The user is then minted Vault shares based on their deposit amount in relation to the total value of the Vault.
- A user can redeem their shares in order to withdraw funds to any address.
- A user can also redeem another user's shares if they have been given an allowance.
- The withdrawer will specify the minimum amount of staking tokens they would like to receive in exchange for their shares.
- When withdrawing, a portion of each of the Vault's underlying asset balances are swapped back for staking tokens based on the percentage of total shares being redeemed.
- This contract is intended to be used behind an upgradeable proxy.
- The Governor and Vault Manager Roles can be transferred by the Governor at any time.
- The Vault Manager can pause the contract at any time, disabling all deposits and withdrawals.
- The Vault Manager or Governor can enable Whitelist-only mode at any time. While enabled, only Whitelisted users can deposit or withdraw from the Vault.
- The Vault Manager or Governor can add or remove any address from the Whitelist at any time.
- The Governor can update the Fee Recipient address at any time.
- The Vault Manager or Governor can update the deposit fee, withdrawal fee, performance fee, and protocol fees to any percentages at any time.
Audit Results
| Vulnerability Category | Notes | Result |
|---|---|---|
| Arbitrary Jump/Storage Write | N/A | PASS |
| Centralization of Control |
|
WARNING |
| Compiler Issues | N/A | PASS |
| Delegate Call to Untrusted Contract | N/A | PASS |
| Dependence on Predictable Variables | N/A | PASS |
| Ether/Token Theft | N/A | PASS |
| Flash Loans | N/A | PASS |
| Front Running | N/A | PASS |
| Improper Events | N/A | PASS |
| Improper Authorization Scheme | N/A | PASS |
| Integer Over/Underflow | N/A | PASS |
| Logical Issues | N/A | PASS |
| Oracle Issues | N/A | PASS |
| Outdated Compiler Version | N/A | PASS |
| Race Conditions | N/A | PASS |
| Reentrancy | N/A | PASS |
| Signature Issues | N/A | PASS |
| Sybil Attack | N/A | PASS |
| Unbounded Loops | N/A | PASS |
| Unused Code | N/A | PASS |
| Overall Contract Safety | PASS |
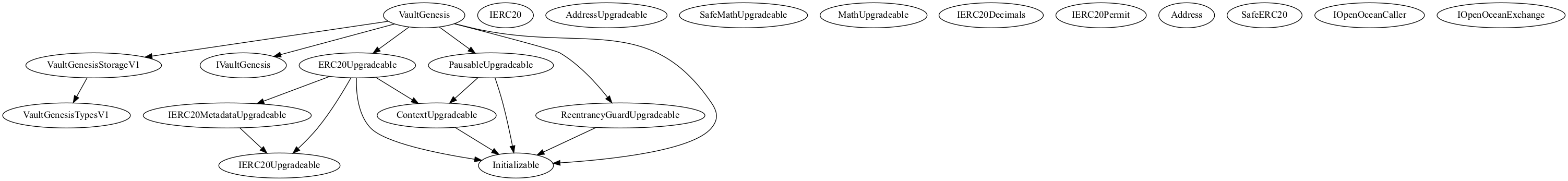
Inheritance Chart
Function Graph
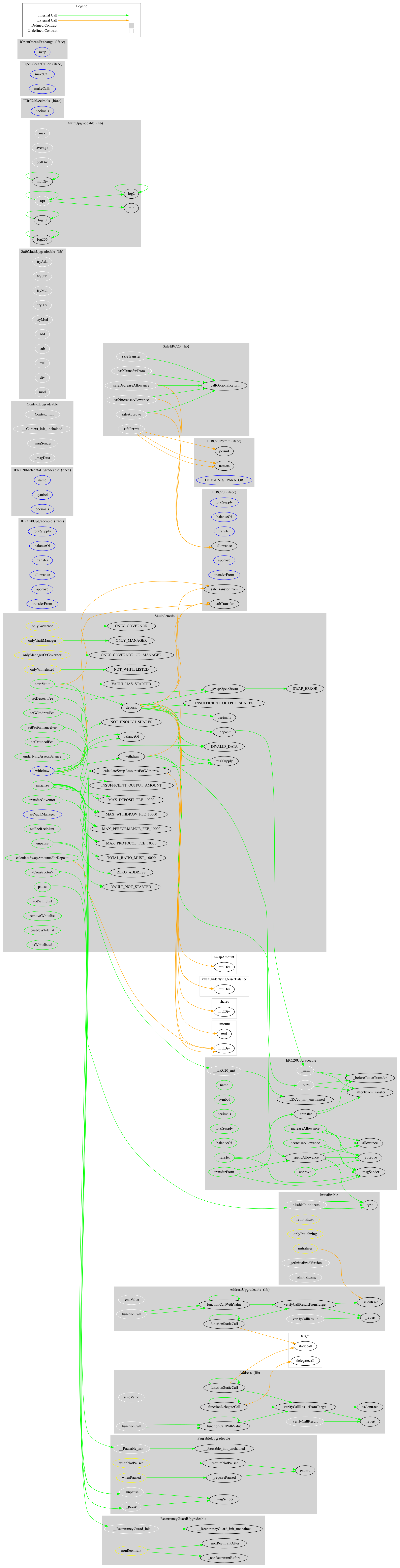
Functions Overview
($) = payable function
# = non-constant function
Int = Internal
Ext = External
Pub = Public
+ [Int] VaultGenesisTypesV1
+ [Int] IERC20
- [Ext] totalSupply
- [Ext] balanceOf
- [Ext] transfer #
- [Ext] allowance
- [Ext] approve #
- [Ext] transferFrom #
+ VaultGenesisStorageV1 (VaultGenesisTypesV1)
+ [Int] IVaultGenesis
+ [Int] IERC20Upgradeable
- [Ext] totalSupply
- [Ext] balanceOf
- [Ext] transfer #
- [Ext] allowance
- [Ext] approve #
- [Ext] transferFrom #
+ [Int] IERC20MetadataUpgradeable (IERC20Upgradeable)
- [Ext] name
- [Ext] symbol
- [Ext] decimals
+ [Lib] AddressUpgradeable
- [Int] isContract
- [Int] sendValue #
- [Int] functionCall #
- [Int] functionCall #
- [Int] functionCallWithValue #
- [Int] functionCallWithValue #
- [Int] functionStaticCall
- [Int] functionStaticCall
- [Int] verifyCallResultFromTarget
- [Int] verifyCallResult
- [Prv] _revert
+ Initializable
- [Int] _disableInitializers #
- [Int] _getInitializedVersion
- [Int] _isInitializing
+ ContextUpgradeable (Initializable)
- [Int] __Context_init #
- modifiers: onlyInitializing
- [Int] __Context_init_unchained #
- modifiers: onlyInitializing
- [Int] _msgSender
- [Int] _msgData
+ ERC20Upgradeable (Initializable, ContextUpgradeable, IERC20Upgradeable, IERC20MetadataUpgradeable)
- [Int] __ERC20_init #
- modifiers: onlyInitializing
- [Int] __ERC20_init_unchained #
- modifiers: onlyInitializing
- [Pub] name
- [Pub] symbol
- [Pub] decimals
- [Pub] totalSupply
- [Pub] balanceOf
- [Pub] transfer #
- [Pub] allowance
- [Pub] approve #
- [Pub] transferFrom #
- [Pub] increaseAllowance #
- [Pub] decreaseAllowance #
- [Int] _transfer #
- [Int] _mint #
- [Int] _burn #
- [Int] _approve #
- [Int] _spendAllowance #
- [Int] _beforeTokenTransfer #
- [Int] _afterTokenTransfer #
+ PausableUpgradeable (Initializable, ContextUpgradeable)
- [Int] __Pausable_init #
- modifiers: onlyInitializing
- [Int] __Pausable_init_unchained #
- modifiers: onlyInitializing
- [Pub] paused
- [Int] _requireNotPaused
- [Int] _requirePaused
- [Int] _pause #
- modifiers: whenNotPaused
- [Int] _unpause #
- modifiers: whenPaused
+ ReentrancyGuardUpgradeable (Initializable)
- [Int] __ReentrancyGuard_init #
- modifiers: onlyInitializing
- [Int] __ReentrancyGuard_init_unchained #
- modifiers: onlyInitializing
- [Prv] _nonReentrantBefore #
- [Prv] _nonReentrantAfter #
+ [Lib] SafeMathUpgradeable
- [Int] tryAdd
- [Int] trySub
- [Int] tryMul
- [Int] tryDiv
- [Int] tryMod
- [Int] add
- [Int] sub
- [Int] mul
- [Int] div
- [Int] mod
- [Int] sub
- [Int] div
- [Int] mod
+ [Lib] MathUpgradeable
- [Int] max
- [Int] min
- [Int] average
- [Int] ceilDiv
- [Int] mulDiv
- [Int] mulDiv
- [Int] sqrt
- [Int] sqrt
- [Int] log2
- [Int] log2
- [Int] log10
- [Int] log10
- [Int] log256
- [Int] log256
+ [Int] IERC20Decimals
- [Ext] decimals
+ [Int] IERC20Permit
- [Ext] permit #
- [Ext] nonces
- [Ext] DOMAIN_SEPARATOR
+ [Lib] Address
- [Int] isContract
- [Int] sendValue #
- [Int] functionCall #
- [Int] functionCall #
- [Int] functionCallWithValue #
- [Int] functionCallWithValue #
- [Int] functionStaticCall
- [Int] functionStaticCall
- [Int] functionDelegateCall #
- [Int] functionDelegateCall #
- [Int] verifyCallResultFromTarget
- [Int] verifyCallResult
- [Prv] _revert
+ [Lib] SafeERC20
- [Int] safeTransfer #
- [Int] safeTransferFrom #
- [Int] safeApprove #
- [Int] safeIncreaseAllowance #
- [Int] safeDecreaseAllowance #
- [Int] safePermit #
- [Prv] _callOptionalReturn #
+ [Int] IOpenOceanCaller
- [Ext] makeCall #
- [Ext] makeCalls ($)
+ [Int] IOpenOceanExchange
- [Ext] swap ($)
+ VaultGenesis (Initializable, ERC20Upgradeable, ReentrancyGuardUpgradeable, PausableUpgradeable, IVaultGenesis, VaultGenesisStorageV1)
- [Pub] #
- [Pub] initialize #
- modifiers: initializer
- [Pub] startVault #
- modifiers: onlyManagerOrGovernor
- [Pub] pause #
- modifiers: onlyVaultManager
- [Pub] unpause #
- modifiers: onlyVaultManager
- [Pub] underlyingAssetsBalance
- [Pub] deposit #
- modifiers: nonReentrant,whenNotPaused,onlyWhitelisted
- [Pub] calculateSwapAmountsForDeposit
- [Int] _deposit #
- [Ext] withdraw #
- modifiers: nonReentrant,whenNotPaused,onlyWhitelisted
- [Int] _withdraw #
- [Pub] calculateSwapAmountsForWithdraw
- [Pub] transferGovernor #
- modifiers: onlyGovernor
- [Ext] setVaultManager #
- modifiers: onlyGovernor
- [Pub] setFeeRecipient #
- modifiers: onlyGovernor
- [Pub] setDepositFee #
- modifiers: onlyManagerOrGovernor
- [Pub] setWithdrawFee #
- modifiers: onlyManagerOrGovernor
- [Pub] setPerformanceFee #
- modifiers: onlyManagerOrGovernor
- [Pub] setProtocolFee #
- modifiers: onlyGovernor
- [Int] _swapOpenOcean #
- [Pub] addWhitelist #
- modifiers: onlyManagerOrGovernor
- [Pub] removeWhitelist #
- modifiers: onlyManagerOrGovernor
- [Pub] enableWhitelist #
- modifiers: onlyManagerOrGovernor
- [Pub] isWhitelisted
About SourceHat
SourceHat has quickly grown to have one of the most experienced and well-equipped smart contract auditing teams in the industry. Our team has conducted 1800+ solidity smart contract audits covering all major project types and protocols, securing a total of over $50 billion U.S. dollars in on-chain value!
Our firm is well-reputed in the community and is trusted as a top smart contract auditing company for the review of solidity code, no matter how complex. Our team of experienced solidity smart contract auditors performs audits for tokens, NFTs, crowdsales, marketplaces, gambling games, financial protocols, and more!
Contact us today to get a free quote for a smart contract audit of your project!
What is a SourceHat Audit?
Typically, a smart contract audit is a comprehensive review process designed to discover logical errors, security vulnerabilities, and optimization opportunities within code. A SourceHat Audit takes this a step further by verifying economic logic to ensure the stability of smart contracts and highlighting privileged functionality to create a report that is easy to understand for developers and community members alike.
How Do I Interpret the Findings?
Each of our Findings will be labeled with a Severity level. We always recommend the team resolve High, Medium, and Low severity findings prior to deploying the code to the mainnet. Here is a breakdown on what each Severity level means for the project:
- High severity indicates that the issue puts a large number of users' funds at risk and has a high probability of exploitation, or the smart contract contains serious logical issues which can prevent the code from operating as intended.
- Medium severity issues are those which place at least some users' funds at risk and has a medium to high probability of exploitation.
- Low severity issues have a relatively minor risk association; these issues have a low probability of occurring or may have a minimal impact.
- Informational issues pose no immediate risk, but inform the project team of opportunities for gas optimizations and following smart contract security best practices.
